1
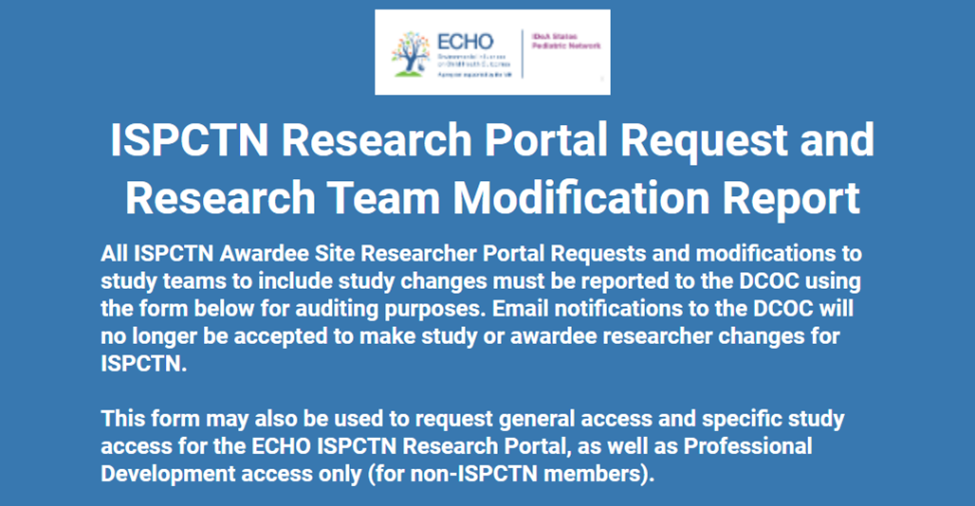
In order to gain access to the ECHO ISPCTN Research Portal, you must request access. Even if others at your institution have access to the portal, you still need to request individual access. By filling out the Portal Request access form, this will start your onboarding process. Access to specific study dashboards must be approved by the DCOC study project lead.
NOTE: If you are not pre-authorized to access the portal and you try to sign in, you will receive a non-approved notification. If you have any questions, email askDCOC@uams.edu
2
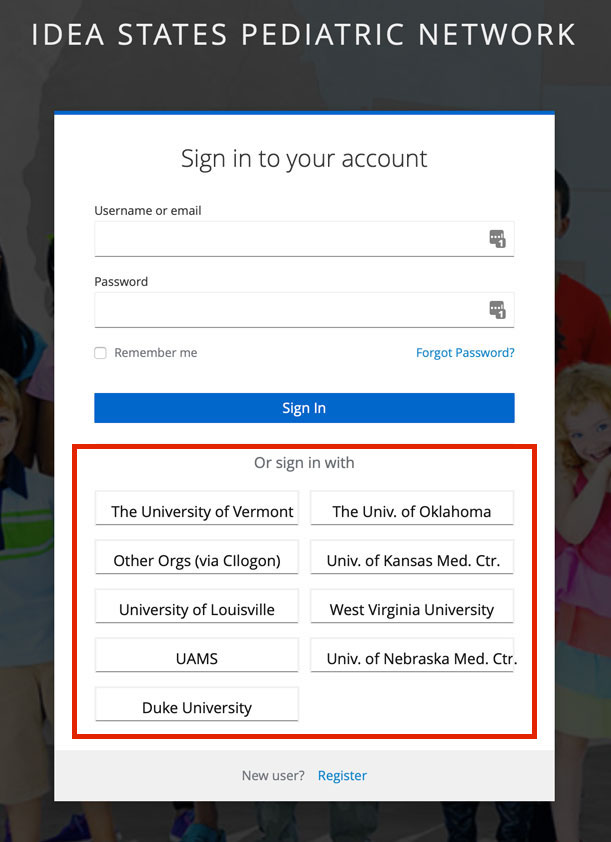
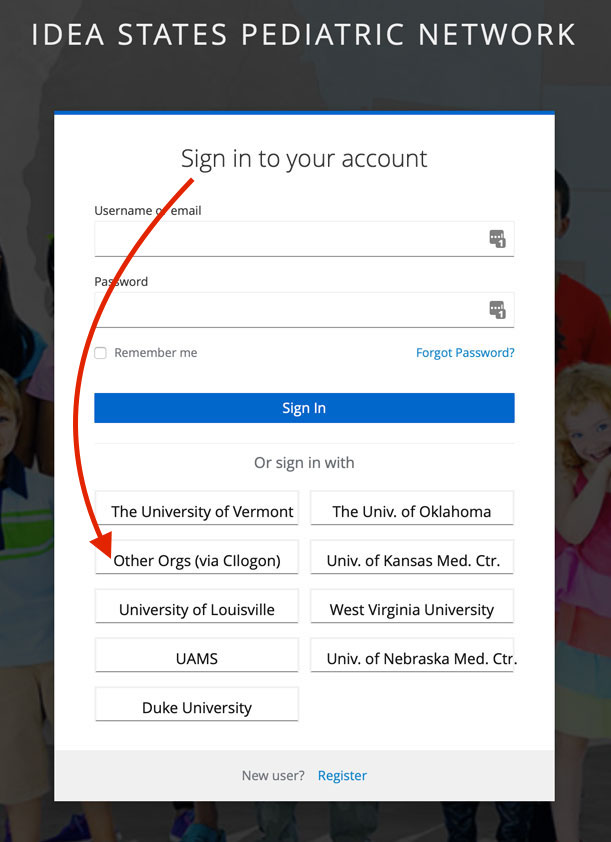
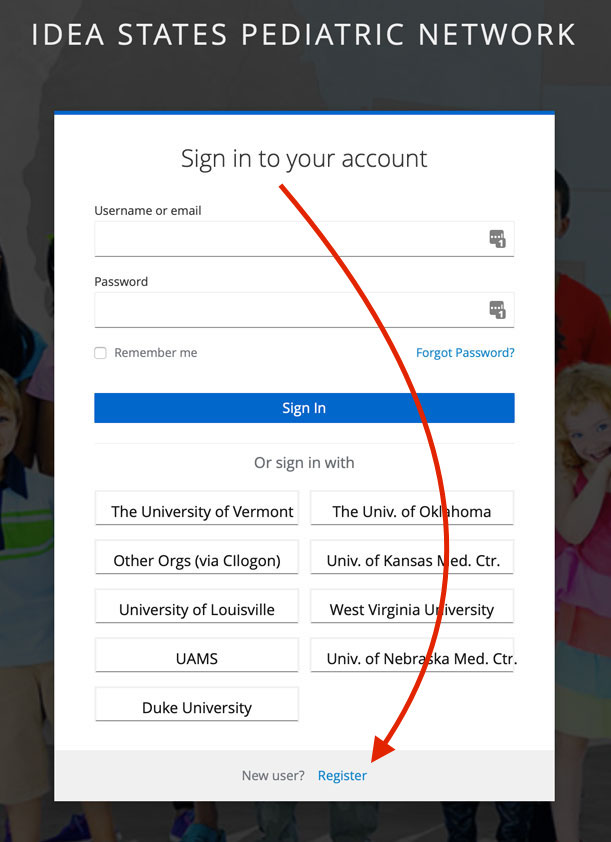
You will receive an email notification once you have been granted access. This email will share instructions on how you can sign into the portal. Look for your institution’s logo in the sign-in process (see screenshot below), select your institution and sign-in using your institutional credentials. If you do NOT see your institution, please choose “All Other Institutions” and enter the credentials we provided you in the approval email you received.
NOTE: Make sure you are using the same email with which you originally requested access (e.g.., jane.doe@univ.edu not jdoe@univ.edu).
Acceptable Use Policy
Prior to account creation, authorized users are required to acknowledge their acceptance of this acceptable use policy (“policy”, “AUP”) before using the ISPCTN Research Portal and associated subsystem (“ISPCTN Portal”, “Portal Services”) operated by the University of Arkansas for Medical Sciences (UAMS) Department of Biomedical Informatics (DBMI) on behalf of the ISPCTN DCOC.
Services provided by the DCOC may only be used for lawful purposes. You agree to comply with all applicable laws, rules, and regulations in connection with your use of the services. Any material or conduct that is determined as a violation of this policy in any manner may result in suspension or termination of the services or removal of user’s account with or without notice. For details on how this policy is enforced, refer to DM-SOP-012 ISPCTN Systems Acceptable Use Enforcement
General Use:
You are responsible for exercising good judgment regarding the reasonableness of personal use. Keep passwords secure and do not share accounts. Authorized users are responsible for the security of their passwords. Only information pertaining to the normal functions of the ISPCTN should be entered into or retrieved from the ISPCTN Portal.
The ISPCTN sites will identify users to be granted access privileges and communicate this information to the DCOC who will grant those users appropriate privileges and authorize their use of the ISPCTN Portal.
Prohibited Use:
You may not use the services to publish content or engage in activity that is illegal under applicable law, that is harmful to others, or that would subject us to liability, including, without limitation, in connection with any of the following, each of which is prohibited under this Acceptable Use Policy:
- Phishing or engaging in identity theft
- Distributing computer viruses, worms, Trojan horses, or other malicious code
- Distributing pornography or adult related content or offering any escort services
- Promoting or facilitating violence or terrorist activities
- Infringing the intellectual property or other proprietary rights of others
- Mining or otherwise engaging in transactions involving cryptocurrencies
Reporting Violations:
All violations and potential violations of this policy are to be reported both internally and externally to the DCOC via the process described in QA-SOP-007 Incident Communication and Escalation
We reserve the right to change this policy at any time. Updates will be posted to the Document Repository on the ISPCTN Portal promptly and flagged to the attention of all Authorized Users.
Oversight & Enforcement:
Oversight of this policy is implemented by DCOC Leadership. This Policy gives Authorized users recourse to appeal to the ISPCTN Leadership Committee in cases where mishandling through DCOC Leadership is suspected.
Entities responsible for detecting violations and policy enforcement processes are specified in DM-SOP-012 ISPCTN Systems Acceptable Use Enforcement.
KeyCloak Single Sign-On Instructions
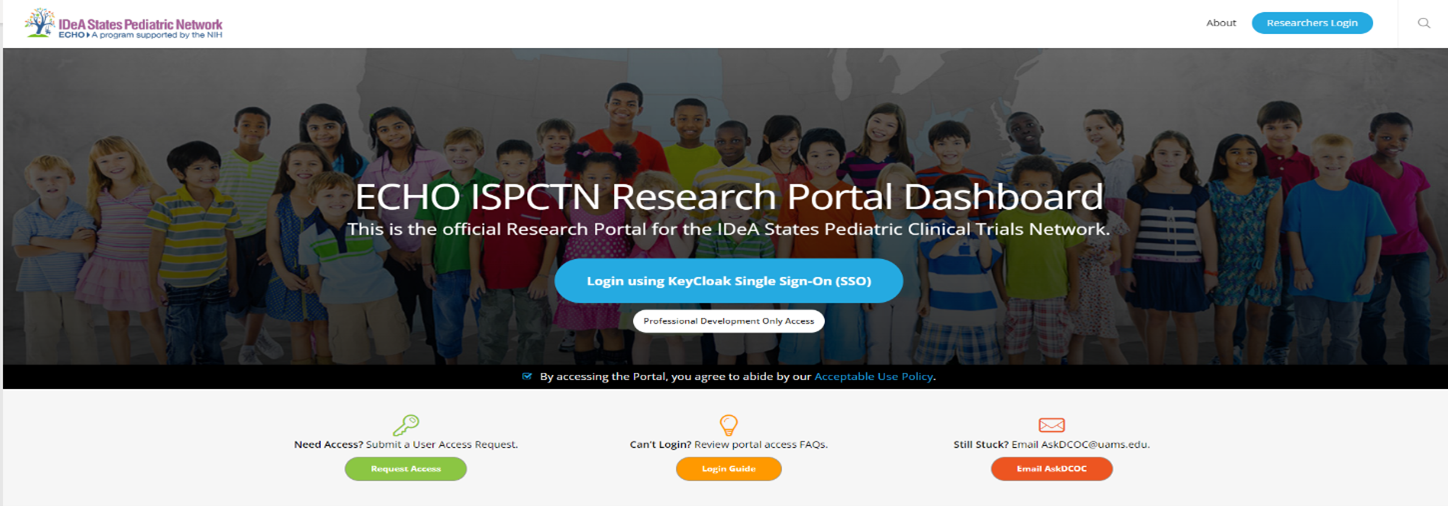
Logging into the Portal using KeyCloak
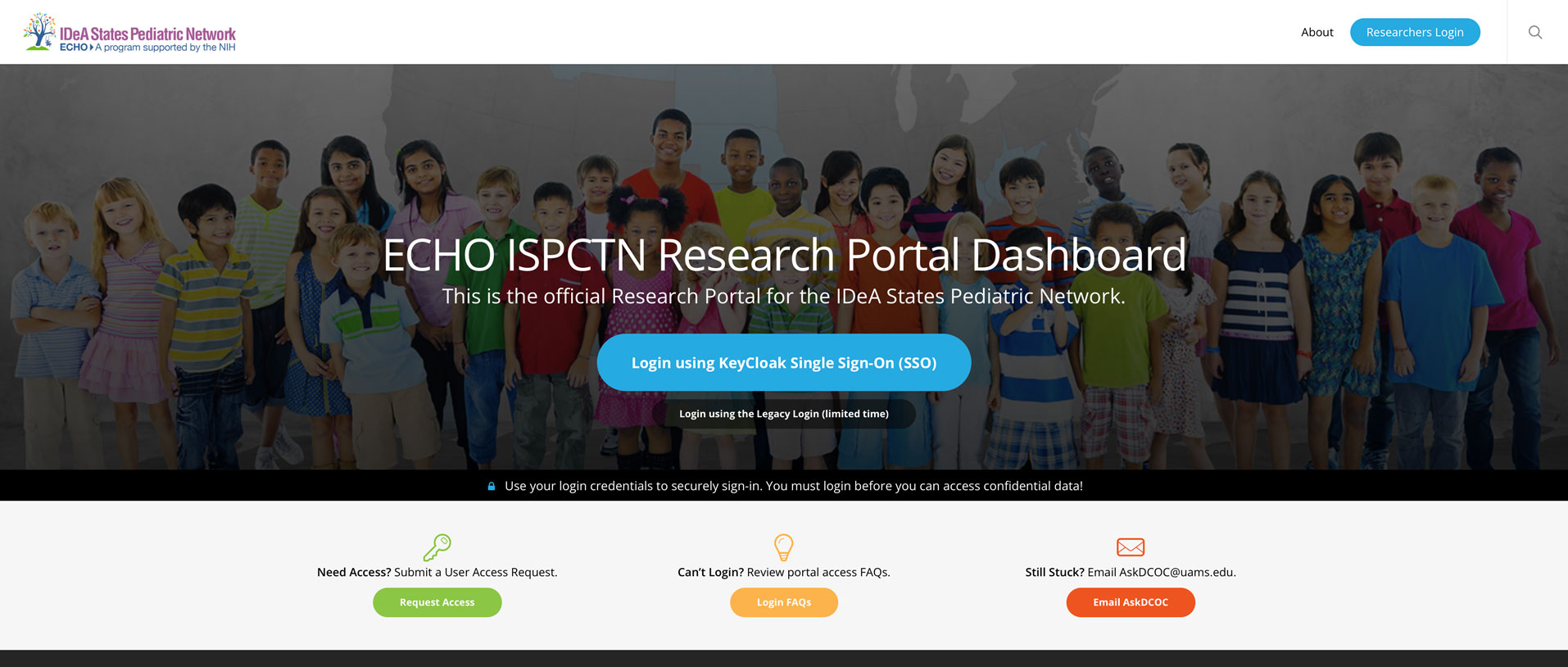
To login using KeyCloak Single Sign-On (SSO), first navigate to the ISPCTN Portal SSO page: https://ideapedtrials.uams.edu/researchers/login
- To login using KeyCloak, the next generation SSO, click the larger blue button.
- Then, proceed to Step 1
NOTE: If you are having trouble logging in using KeyCloak, you can login to Professional Development by clicking on the smaller white button.
Table of Contents
- How to Login using KeyCloak from the Portal
- Option 1: Login using your Institutional credentials
- Option 2: Login using CI Login (Google, ORCID, eduGAIN, etc.)
- Option 3: Login using an internal KeyCloak account
- Troubleshooting OpenClinica access error(s)
Login using your institutional credentials
This is the most efficient method of logging in to the Portal. If you see your institution listed at the KeyCloak login screen (see figure 1), click on your institutional name and use your institutional login credentials.
If you do not see your institution listed, proceed to Step 2.
Login using CI Login (Google, InCommon, ORCID, etc.)
CI Login is perhaps the most flexible method of logging in to the Portal. You have the option of using the following:
- – A Google account (email must match your institutional email address)
- – An ORCID account*
- – An InCommon account
- – An eduGAIN account
- – and many other.
* If you do not have an ORCID account, you can sign-up for one at the ORCID login screen.
If you are unable to login using CI Login, proceed to Step 3.
Login using an Internal KeyCloak Account
This option has no restrictions, except you must manage a new password.
NOTE: Unless you use the same email address you used previously to access the Portal (or that was submitted in your UAR), this new account won’t link to your original account or the account you are being assigned.
If you are unable to login using this method, please contact AskDCOC on the DCOC help desk.
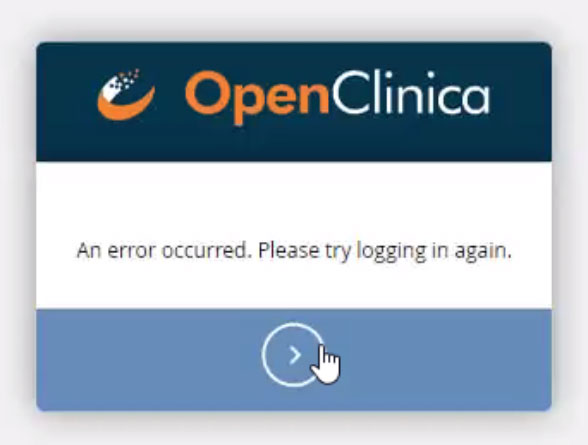
Encountering an error when logging into OpenClinica
Some users see an error message after logging in through KeyCloak. To remedy this, simply.
- 1. Close the browser window.
- 2. Reopen the browser and login back in.
This time you should be able to access OpenClinica. If you still experience any issues, please contact AskDCOC.